Unlocking Cybersecurity: A Deep Dive into Threat Intelligence Data
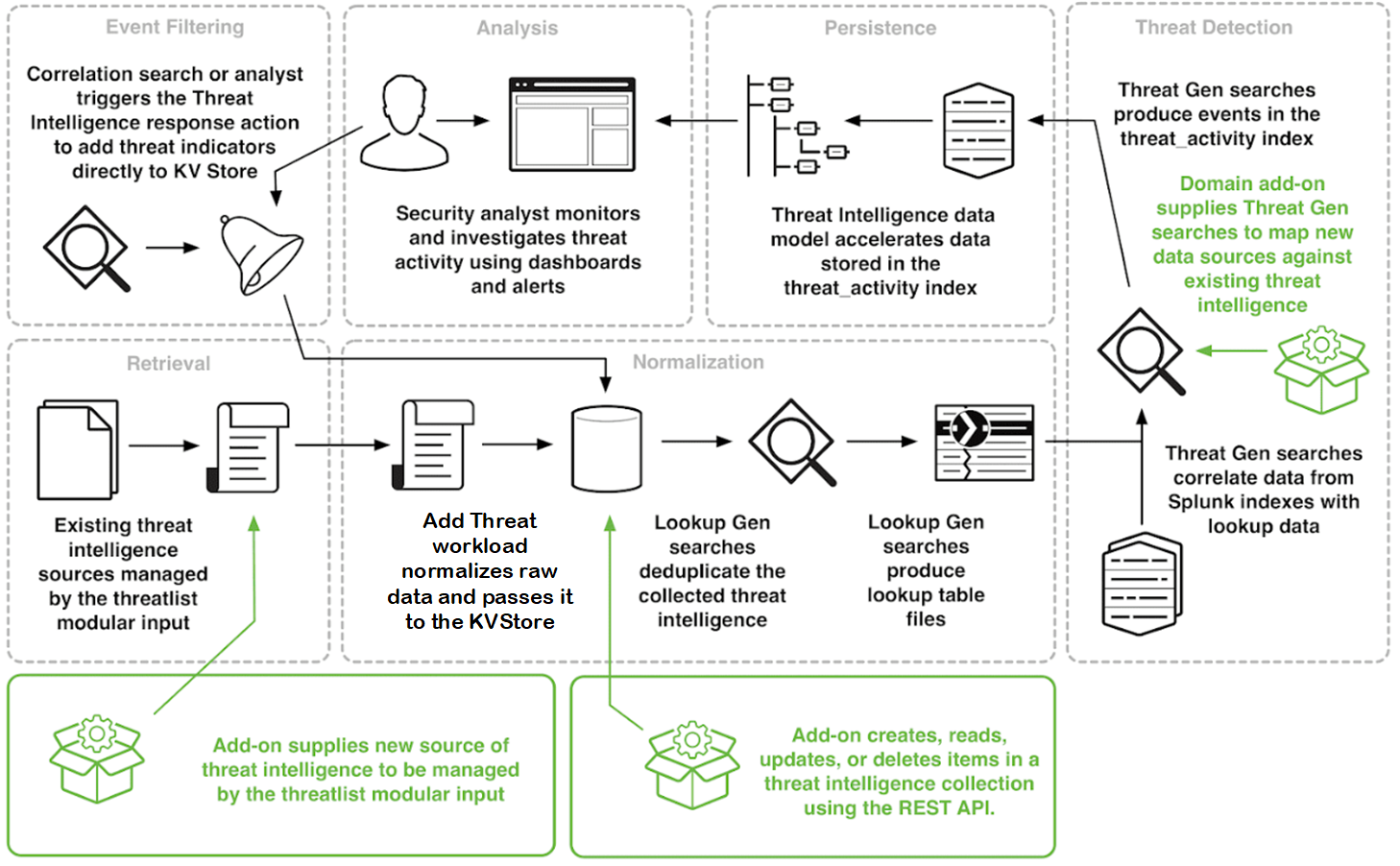
Unlocking Cybersecurity: A Deep Dive into Threat Intelligence Data In today’s complex digital landscape, organizations face an ever-increasing barrage of cyber threats. From sophisticated ransomware attacks to insidious phishing campaigns, the risks are multifaceted and constantly evolving. To effectively defend against these threats, businesses are increasingly turning to threat intelligence data. This article provides a … Read more