Unlocking Cybersecurity: A Deep Dive into Threat Intelligence Data
In today’s complex digital landscape, organizations face an ever-increasing barrage of cyber threats. From sophisticated ransomware attacks to insidious phishing campaigns, the risks are multifaceted and constantly evolving. To effectively defend against these threats, businesses are increasingly turning to threat intelligence data. This article provides a comprehensive overview of what threat intelligence data is, its various types, how it’s collected and analyzed, and how organizations can leverage it to bolster their cybersecurity posture.
What is Threat Intelligence Data?
Threat intelligence data is information that helps organizations understand the threats they face. It goes beyond simply identifying malware or intrusion attempts; it provides context, including who is behind the attacks, their motivations, and their methods. This understanding allows organizations to proactively defend against attacks and mitigate the impact of successful breaches.
Think of it as a detective gathering clues to solve a case. The clues, in this case, are pieces of information about cyber threats. The detective (the security team) analyzes these clues to understand the bigger picture and anticipate the attacker’s next move. Effective use of threat intelligence data transforms a reactive security posture into a proactive and resilient one.
Types of Threat Intelligence Data
Threat intelligence data comes in various forms, each providing unique insights into the threat landscape. Understanding these types is crucial for effectively utilizing threat intelligence.
Technical Threat Intelligence
This type focuses on indicators of compromise (IOCs). IOCs are pieces of forensic data that identify potentially malicious activity on a network or system. Examples of technical threat intelligence data include:
- IP addresses of malicious servers
- Domain names used in phishing campaigns
- File hashes of malware samples
- Network traffic signatures
Technical threat intelligence data is typically used for automated detection and response. Security tools, such as intrusion detection systems (IDS) and security information and event management (SIEM) systems, can be configured to automatically block or alert on IOCs.
Tactical Threat Intelligence
Tactical threat intelligence data focuses on the tactics, techniques, and procedures (TTPs) used by threat actors. It describes how attackers operate, including the tools they use, the methods they employ, and the steps they take to achieve their objectives. Understanding TTPs allows organizations to anticipate and defend against attacks more effectively. For example, knowing that a particular group uses spear phishing emails with malicious attachments allows security teams to train employees to identify and avoid these types of attacks.
Strategic Threat Intelligence
Strategic threat intelligence data provides a high-level overview of the threat landscape. It focuses on the motivations, capabilities, and intentions of threat actors. This type of intelligence is typically used by senior management and security leaders to make strategic decisions about security investments and risk management. For instance, strategic intelligence might reveal that a particular industry is being targeted by a nation-state actor, prompting the organization to increase its security budget and implement stricter security controls. [See also: Cybersecurity Risk Management]
Operational Threat Intelligence
Operational threat intelligence data focuses on specific attacks that are currently underway or are likely to occur in the near future. This type of intelligence is often used by security operations center (SOC) analysts to respond to incidents and prevent future attacks. For example, operational intelligence might reveal that a particular vulnerability is being actively exploited, prompting the organization to patch the vulnerability immediately.
Collecting Threat Intelligence Data
Collecting threat intelligence data is a complex process that involves gathering information from a variety of sources. These sources can be broadly categorized as follows:
- Open-Source Intelligence (OSINT): This includes information that is publicly available on the internet, such as news articles, blog posts, social media feeds, and security reports. OSINT is a valuable source of information about emerging threats and vulnerabilities.
- Commercial Threat Intelligence Feeds: These are subscription-based services that provide access to curated threat intelligence data from security vendors and research organizations. These feeds typically include IOCs, TTPs, and other information about threat actors and their activities.
- Internal Threat Intelligence: This includes information gathered from within the organization, such as security logs, incident reports, and vulnerability assessments. Internal threat intelligence data can provide valuable insights into the organization’s specific threat profile.
- Information Sharing and Analysis Centers (ISACs): ISACs are industry-specific organizations that facilitate the sharing of threat intelligence among their members. These centers provide a valuable forum for collaboration and information exchange.
Analyzing Threat Intelligence Data
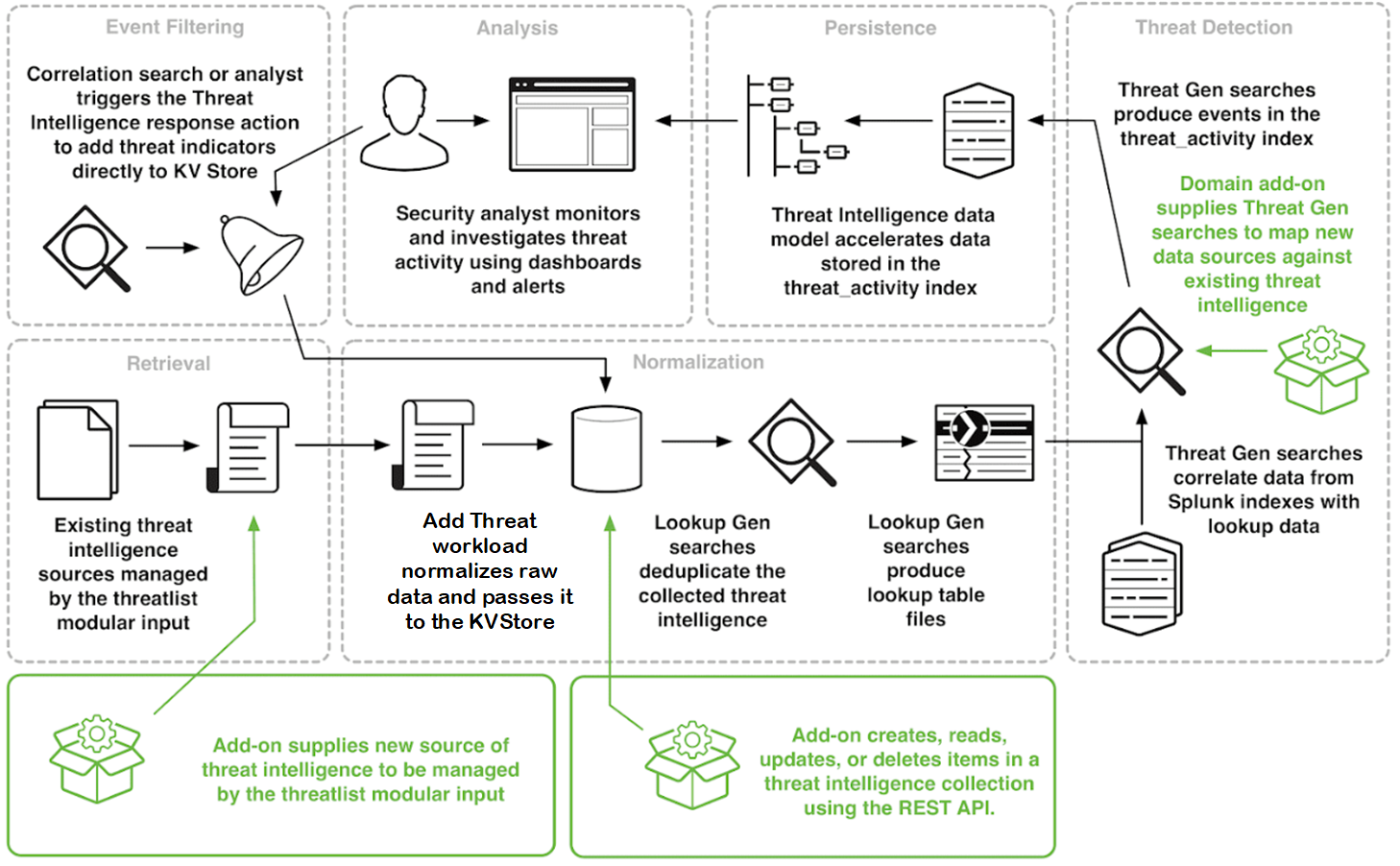
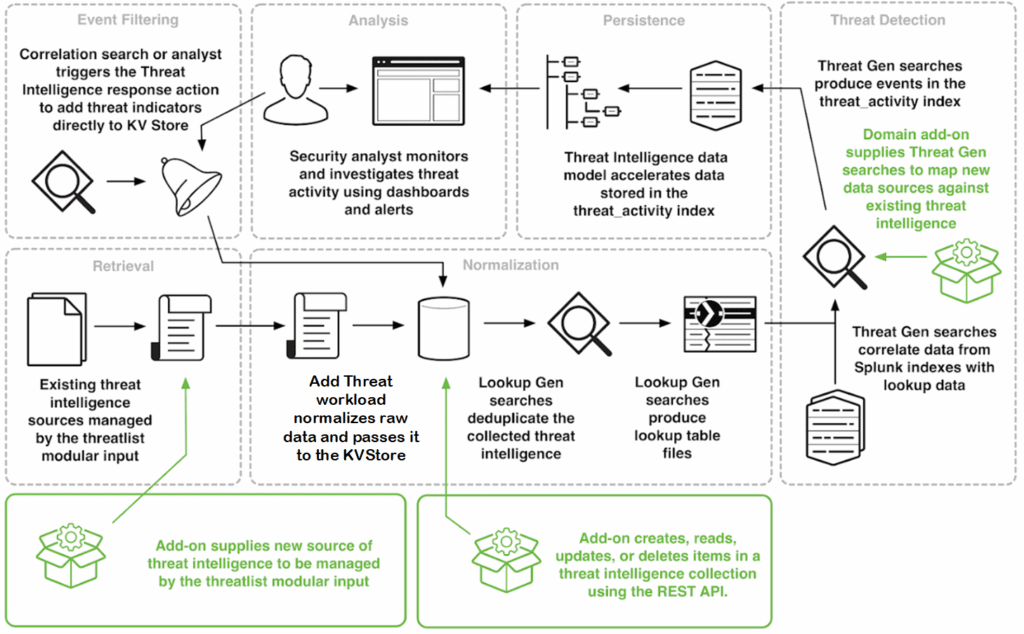
Once threat intelligence data has been collected, it must be analyzed to extract meaningful insights. This process typically involves the following steps:
- Data Aggregation: Gathering data from various sources and consolidating it into a central repository.
- Data Enrichment: Adding context to the data by correlating it with other sources of information. For example, enriching an IP address with geolocation data can help determine the origin of an attack.
- Data Analysis: Identifying patterns and trends in the data to understand the threat landscape. This may involve using techniques such as statistical analysis, machine learning, and data visualization.
- Reporting and Dissemination: Communicating the findings to relevant stakeholders in a clear and concise manner. This may involve creating reports, dashboards, and alerts.
Leveraging Threat Intelligence Data for Cybersecurity
The ultimate goal of threat intelligence data is to improve an organization’s cybersecurity posture. Here are some ways organizations can leverage threat intelligence:
- Proactive Threat Detection: Using IOCs and TTPs to proactively identify and block malicious activity before it can cause damage.
- Incident Response: Using threat intelligence to quickly and effectively respond to security incidents. This may involve identifying the source of the attack, containing the damage, and preventing future attacks.
- Vulnerability Management: Using threat intelligence to prioritize vulnerability patching based on the likelihood of exploitation.
- Security Awareness Training: Using threat intelligence to educate employees about the latest threats and how to avoid them.
- Risk Management: Using strategic threat intelligence data to inform risk management decisions and prioritize security investments.
Challenges in Implementing Threat Intelligence
While threat intelligence data offers significant benefits, implementing it effectively can be challenging. Some of the key challenges include:
- Data Overload: The sheer volume of threat intelligence data can be overwhelming. Organizations need to be able to filter and prioritize the most relevant information.
- Data Quality: The quality of threat intelligence data can vary significantly. Organizations need to be able to validate the accuracy and reliability of the data.
- Integration: Integrating threat intelligence data with existing security tools and processes can be complex. Organizations need to ensure that their tools can consume and utilize threat intelligence effectively.
- Lack of Expertise: Analyzing and interpreting threat intelligence data requires specialized skills and expertise. Organizations may need to invest in training or hire dedicated threat intelligence analysts.
- Cost: Implementing a comprehensive threat intelligence program can be expensive. Organizations need to carefully evaluate the costs and benefits before making an investment.
Best Practices for Threat Intelligence
To overcome these challenges and maximize the benefits of threat intelligence data, organizations should follow these best practices:
- Define Clear Objectives: Clearly define the goals and objectives of the threat intelligence program. What specific threats are you trying to address? What information do you need to make informed decisions?
- Choose the Right Sources: Select threat intelligence data sources that are relevant to your organization’s industry, geography, and threat profile.
- Automate Where Possible: Automate the collection, analysis, and dissemination of threat intelligence data to improve efficiency and reduce manual effort.
- Integrate with Existing Security Tools: Integrate threat intelligence data with your existing security tools, such as SIEM, IDS, and firewalls, to improve threat detection and response capabilities.
- Continuously Monitor and Evaluate: Continuously monitor and evaluate the effectiveness of your threat intelligence program. Are you meeting your objectives? Are you getting the right information? Make adjustments as needed.
The Future of Threat Intelligence Data
The field of threat intelligence data is constantly evolving. As cyber threats become more sophisticated, so too must the methods used to detect and prevent them. Some of the key trends shaping the future of threat intelligence include:
- Artificial Intelligence (AI) and Machine Learning (ML): AI and ML are being used to automate the analysis of threat intelligence data and identify patterns that would be difficult or impossible for humans to detect.
- Threat Hunting: Threat hunting is a proactive approach to security that involves actively searching for threats that have evaded traditional security controls. Threat intelligence data is a critical component of threat hunting.
- Cyber Threat Intelligence Platforms (CTIPs): CTIPs are platforms that provide a centralized repository for threat intelligence data and tools for analyzing and sharing information.
- Increased Collaboration: Increased collaboration among organizations and governments is essential for sharing threat intelligence data and combating cybercrime.
Conclusion
Threat intelligence data is an essential component of a modern cybersecurity program. By understanding the threats they face, organizations can proactively defend against attacks, mitigate the impact of successful breaches, and improve their overall security posture. While implementing a threat intelligence program can be challenging, the benefits far outweigh the costs. By following best practices and staying abreast of the latest trends, organizations can leverage threat intelligence data to stay one step ahead of cybercriminals and protect their valuable assets. The continuous evolution of threat intelligence data and its application, especially with advancements in AI and ML, promises a more robust and proactive defense against the ever-changing landscape of cyber threats. Understanding and utilizing this data effectively is no longer an option but a necessity for organizations striving to maintain a secure digital environment. [See also: Incident Response Planning]